© Copyright 2023 Constellation GovCloud®. All rights reserved.
Cloud computing is the present and the future for information technology (IT). And while the commercial market may be ahead of the curve for its adoption, the federal government is following closely behind. Of the $100 billion spent on information technology (IT) by the U.S. government in 2022 – a whopping $12 billion went to cloud services – a number that is sure to increase in the coming years. This isn’t a surprise given the 2020 survey of government IT decision makers that showed 91 percent of federal respondents report having “all, most, or some systems and solutions in the cloud.”
The incorporation of cloud solutions in federal enterprise systems is booming as government agencies continue to retire their legacy applications and look to the rapidly growing catalog of cloud solutions to modernize their IT operations. Whether driven by the Office of Management and Budget’s (OMB’s) “Cloud Smart” policy, the increasing availability of government community clouds, cloud-based platforms and applications like Zoom for Government, or the availability, flexible pricing, resilience, and agility generally afforded by cloud services, cloud-based “as-a-service” solutions are here to stay – and play an essential role in government operations.
FedRAMP Authorization – Required for any Cloud Service used by Federal Agencies
Before any cloud solution, including software-as-a-service (SaaS) applications can be used by a federal agency, they must first achieve FedRAMP Authorization to Operate (ATO). Established as a program in 2012 and codified into law in 2022, FedRAMP provides a standardized approach to security and risk assessment for cloud technologies and federal agencies, helping promote the adoption of secure cloud services across the government. Each system must comply with a baseline (low, moderate or high) that aligns with the sensitivity of data handled in that system. The majority of SaaS solutions serving government agencies will handle or process data that meets the FIPS 199 criteria for a moderate impact level, meaning those systems would handle Controlled Unclassified Information (CUI), or government data that is not publicly available. For those systems, this means strict compliance with 323 security baseline controls spanning 18 NIST 800-53 (Rev. 5) control families.
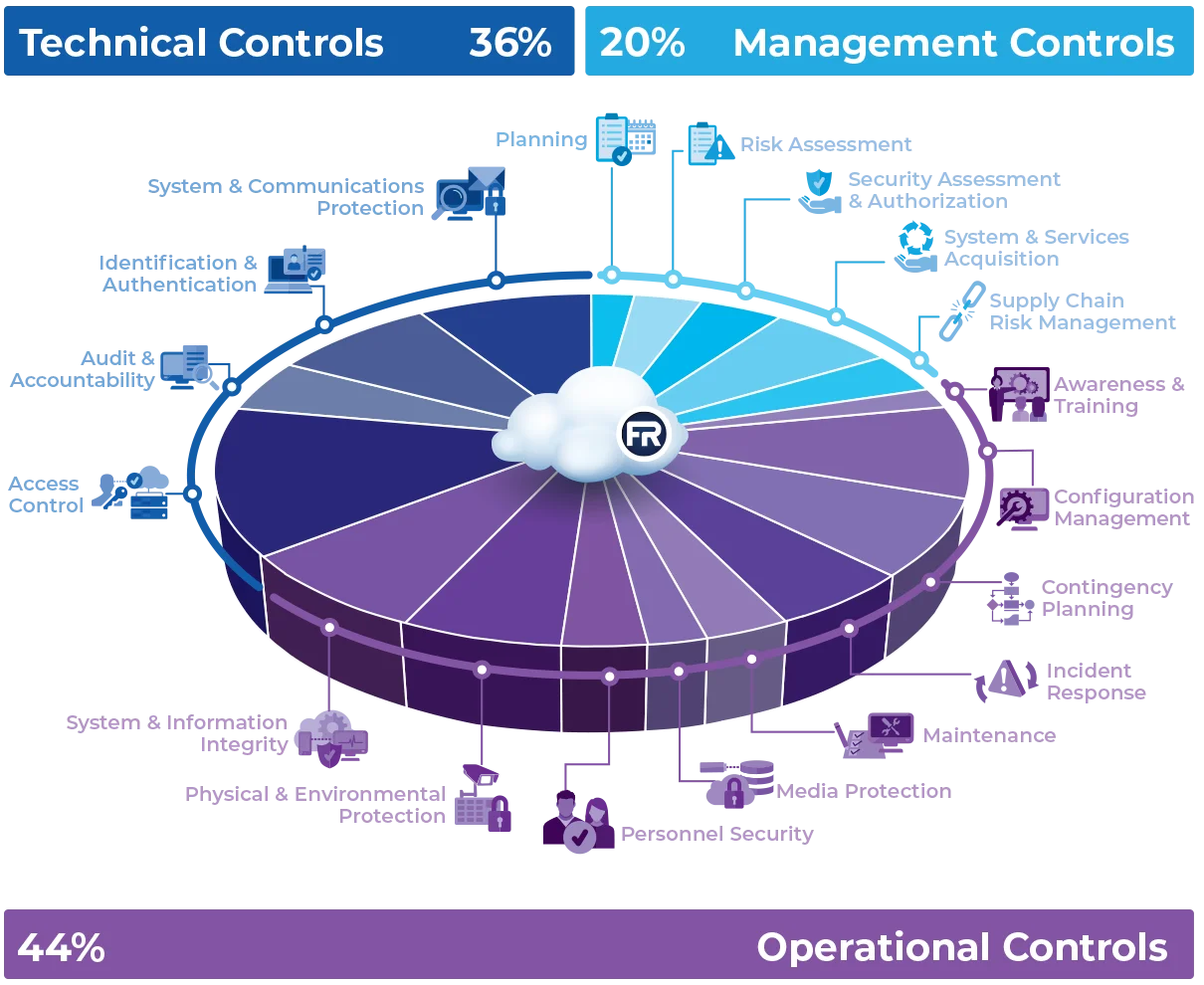
FedRAMP Focuses on Operational and Management Maturity
Any way you look at it, 323 security controls is a lot. And if you think that all 323 can be handled by technology implementations and configurations, keep reading. The fact is, FedRAMP controls are as much or more about the management and operational maturity surrounding a SaaS offering than the technology itself. That’s not to say that things like FIPS validated encryption, access control and user authentication technologies don’t matter – they do! However, nearly two-thirds of the FedRAMP Moderate controls deal directly with Management and Operations.
Getting your House in Order for FedRAMP
Before jumping head-first into a FedRAMP authorization effort, you must understand what that commitment looks like for your technical, operational and management teams. Being prepared both technically and operationally will make the authorization process go much smoother (and faster) and pave the way to securing a government agency sponsor. Agency sponsorship is required for the majority of FedRAMP authorization efforts – the exception being the handful of SaaS providers who secure a provisional authorization slot with the Joint Authorization Board – which is a topic for another blog post.
-
Consider Technical Readiness
It is best to do some research (or engage with a knowledgeable advisor) as a first step to identify showstopping technical issues that would preclude your SaaS solution from obtaining a FedRAMP authorization. Understanding requirements around your offering’s technical authorization boundary, network segmentation, potential reliance on non-compliant libraries, or connections to external systems are just a few areas that must be scrutinized and possibly adjusted to meet FedRAMP’s technical control requirements.
-
Consider Operational Readiness
Building and maintaining a FedRAMP compliant SaaS offering has implications for software operations teams (architects, developers, testers, configuration managers, change control board, etc.) and deployment schedules, as well as human resources, corporate IT, Facility Security Officers (FSOs), project management, documentation management, facilities management, and even legal counsel. Members of these teams will likely be tagged to satisfy critical roles and be required to take on FedRAMP-specific responsibilities.
Maintaining FedRAMP compliance is also reliant on having people assigned to roles with skillsets that existing members of a software development team or the broader organization may not possess, such as an Information Systems Security Manager (ISSM) and an Information Systems Security Officer (ISSO). These roles require subject matter expertise in security controls and compliance program requirements, as well as attestable commitment to staying up-to-date on compliance and regulatory changes. For companies taking full ownership over their FedRAMP system, this means an investment in hiring, training, and supervision.
In addition to staffing impacts, operational readiness also means having mature employee and security-management processes and procedures and a framework for managing those processes and procedures that can be readily adapted to incorporate the unique FedRAMP operational requirements. With hundreds of pages of documented policies, procedures, and plans required for FedRAMP, implementation oversight can be overwhelming.
-
Consider Management Readiness
Finally, organizations that aspire to obtain FedRAMP authorization need to have strong in-house product and program management skills. With many moving parts including multiple purpose-defined teams and related issue identification and resolution processes, strong management skills are imperative. Ongoing close and often prescribed collaboration with the sponsor government agency and the FedRAMP PMO are fundamental to the compliance and continuous monitoring process. FedRAMP systems don’t run and maintain compliance on their own, so it’s important to invest in the right product and program management personnel.